4.7.3. Architecture
In this section we talk about the 2SRA basic architecture: the components, the simplified architecture and the recommended sizing.
4.7.3.1. Components
2SRA module deployment requires the installation of some components. One or more Frontend (VPN Gateway) and a Backend composed of four additional components; centralized management of the solution, the integration and users authentication with the corporate identity manager, the management of the GAuth OTP, the centralization of logs, traffic monitoring, among others.
4.7.3.1.1. ON Core
ON Core provides the centralized management console of the solution. It is where the Visibility policy engine for discovery resides. This device runs the logic that processes and validates asset profiling based on multiple conditions and characteristics. It also runs plugins to enrich profiling in a active or passive way.
It is a mandatory component of the solution and includes critical components such as:
Policy Engine: It is the solution’s brain. All modules are implemented using this component.
CMDB: It is the memory of the solution where all the configuration, assets and its features are saved.
The administration portal is the control panel for the solution.
Note
It is a critical component in the solution. The implementation of one or more nodes will depend on the requirements of the deployment, and the final architecture design to provide high availability.
With this component offline, we would lose the ability to stablish VPN connections, authenticate users, etc.
4.7.3.1.2. ON Analytics
ON Analytics is based on the ELK Stack, receives the platform logs, structures, metadata and builds the datalake to show dashboards and reports in real time to allows the specific searches.
It is a mandatory component of the solution that includes non-critical components such as:
Aggregator: an enrichment of all the information generated by any component of OpenNAC Enterprise.
Search Engine: based on an elastic search engine that allows you to easily search the information generated and collected by the OpenNAC Enterprise components.
Dashboards and reports: The solution includes a set of dashboards and reports based on common technical information gathered. You can create and generate your own custom dashboards.
Note
ON Analytics is a non-critical component for the solution, therefore, it does NOT require high availability. The implementation of one or more nodes will depend on the requirements of the deployment, and the final architecture design. If this component is outlined, the main functionality of OpenNac Enterprise modules would continue working, with the exception that during the outlined period we would no longer have the ability to process and display the information of the solution.
In deployments where a large amount of data is generated, it may be necessary to deploy multiple Analytics nodes to load balancing the storage. Analytics has two types of roles, typically within the same node, a role with aggregation functions (Aggregator) that receives information through Filebeat and process logs with Logstash, the other role (Analytics) with data management functions performed by ElasticSearch and visualization through Kibana.
4.7.3.1.3. ON Agent
The Agent is a software that is installed in the end for VPN connection establishment, monitoring and the hardware/software posture of the device. It is required for the Secure Remote Access (2SRA) module.
Allows you to manage and perform a detailed analysis of the device inventory (for example, OS patches, health and security features, deployed applications, etc.)
Establishment of the VPN tunnel, and validation of credentials using 2FA. 3. ON Agent
4.7.3.1.4. ON Sensor
ON Sensor is based on IDS technology, it processes the traffic generated in the network. Performs a deep analysis of network protocols that are being used by ingesting the traffic through a port-mirror (SPAN, RSPAN or ERSPAN).
It is an optional component that provides:
Network Behavior Monitoring. Provides metadata of network traffic that is captured by copying the traffic through the port-mirror configured on the network device. It is capable of decoding multiple standard protocols and applications, providing information from layer 2 to layer 7.
Note
ON Sensor is is a non-critical component for the solution, therefore, it does NOT require high availability. If this component is outlined, the main functionality of OpenNAC Enterprise modules would continue working, with the exception that during the outlined period we would no longer have the ability to have advanced visibility, analysis and monitoring of network behavior.
4.7.3.1.5. VPN Gateway
The VPN Gateway provides the ability to establish the VPN from a remote location to the corporate network, as well as apply segmentation access policies, depending on the user profile. The management for VPN Gateway requires an additional machine, the CMI console, which allows the centralized management of all the VPN Gateway nodes.
It is a mandatory component for the Secure Remote Access (2SRA) module, which includes critical components such as:
Policy Enforce: Stateful Firewall module that allows the definition and execution of access rules, based on IP, port source and destination.
VPN Roadwarior: It allows the configuration of the VPN Gateway, authentication, encryption, pool of IP addresses, internal networks, dynamic zones, etc.
Traffic Log Monitor: Using Filebeat (ELK) the accepted or denied Firewall traffic logs are sent to the CMI management console for its visualization.
Note
It is a critical node in the solution and high availability deployment is recommended. The deployment of one or more nodes to provide high availability will depend on the deployment requirements, and the final architecture design. With this module offline we would lose the ability to establish VPN connections
4.7.3.1.6. CMI
The CMI console, allows the remote centralized updating management of the VPN Gateways. It maintains the system update packages and the object base (networks, hosts, protocols, means of authentication, etc.) to distribute among the different VPN Gateways, in addition to centralizing LOGs to view them graphically.
It is a mandatory component for the Secure Remote Access 2SRA module, which includes non-critical components such as:
The CMDB is the memory of the solution where all the configuration, assets and parameterization are saved.
Aggregation and enrichment of all the information generated by any VPN Gateway.
The Administration Console is the control panel for the solution.
dnf Repository, rpm package repository used as an installation and update source.
Note
CMI is is a non-critical component for the solution, therefore, it does NOT require high availability. If this component offline, the VPN will continue to work. With an exception that during the downtime we would no longer have the ability to configure, update and monitor / analyze the Firewall records of accepted or denied traffic
4.7.3.2. Standard Architecture
A reference architecture requires the components described above and depends on the network architecture available to the customer, as well as the number of end users on the network. Based on the criticality of the components and location in the network, the following should be considered points:
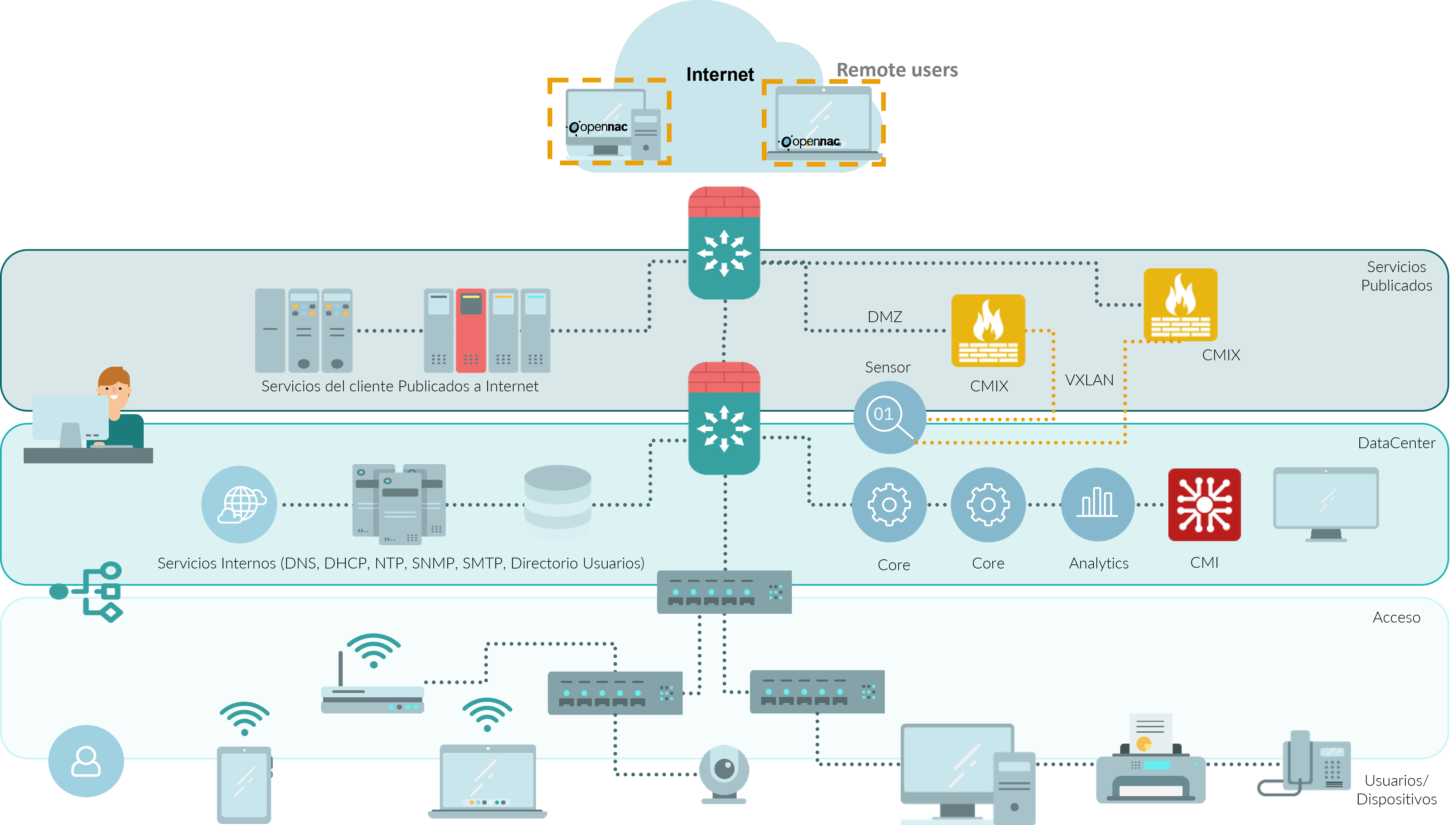
The VPN Gateway needs to have internet access for clients to connect. It is the one and only component that requires being exposed in the internet, and it is recommended to install it in a DMZ network separate from the published, internal servers, and the others solution components. Below,you can see an architecture showing the nodes and components suggested location.
Note
Deployment in high availability will depend on the customer’s requirements. If a HA deployment is required, it will be necessary to add additional components (two or more VPN Gateways).
4.7.3.3. Standard Sizing
Based on the reference architecture, the standard sizing of the solution for 2SRA module to support up to 1.500 network users and average traffic of 400kbp will be:
4.7.3.3.1. Sizing
Concurrent user growth is achieved by adding more nodes in an N + 1 scheme through a RADIUS proxy or load balancer.
Component |
Number |
CPU |
Memory |
Disc/Type |
Network Int. |
|---|---|---|---|---|---|
VPN Gateway (Frontend) |
4 Cores |
8 GB |
100 GB/SSD |
2 NIC** |
|
ON Core |
8 Cores |
16 GB |
160 GB/SSD |
2 NIC** |
|
ON Analytics |
8 Cores |
16 GB |
300 GB/SSD |
2 NIC** |
|
ON Sensor |
8 Cores |
16 GB |
100 GB/SSD |
|
|
CMI |
4 Cores |
8 GB |
100 GB/SSD |
2 NIC** |
|
ON Agent |
N |
Note
** The 2 network interfaces are mainly for service and management (internal communication between the different nodes)
*** In some cases, it is recommended to have at least 2 NICs for active-passive port-span.